by David Marshall | Dec 21, 2020 | DaaS, Desktop Virtualization, End User Computing
WhatMatrix: The coronavirus pandemic has accelerated virtual desktop sales momentum. What are some of the big questions you are being asked to answer from companies shifting to work from home, and how are you answering those questions? How fast can I get there?... 
by David Marshall | Sep 4, 2020 | DaaS, DaaS, EUC, Everything else ...
WhatMatrix: The coronavirus pandemic has accelerated virtual desktop sales momentum. What are some of the big questions you are being asked to answer from companies shifting to work from home, and how are you answering those questions? VMware: The pandemic has... 
by Michael Dehoyos | Aug 24, 2020 | Affiliate Article, CMPs, Public Cloud
There are endless reasons why your organisation may what to start implementing a multi-cloud strategy, many of which include increased productivity, lower operating costs, and the freedom to benefit from all the cloud options available. However, setting up and using a... 
by Community Author | Jul 5, 2020 | Application Layering, DaaS, DaaS, End User Computing, EUC, Everything else ...
Adam Lotz of Citrix Shares Expertise and Advice on Virtual Desktops, Security and Work From Home WhatMatrix: The coronavirus pandemic has accelerated virtual desktop sales momentum. What are some of the big questions you are being asked to answer from... 
by Leslie Dye | Jun 16, 2020 | DaaS, Desktop Virtualization, EUC, Universal Device Management
It is becoming increasingly critical in the current data-driven world to find the right computing resources for your business. The post-pandemic era demands companies to be flexible while not compromising on productivity. One of the significant changes we saw in... 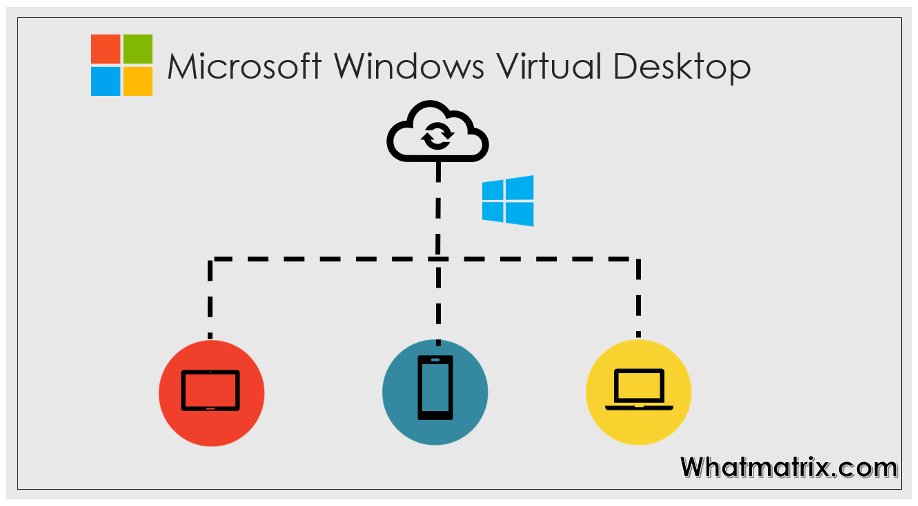
by Ajay Walia | Jun 3, 2020 | DaaS, Desktop Virtualization, Public Cloud
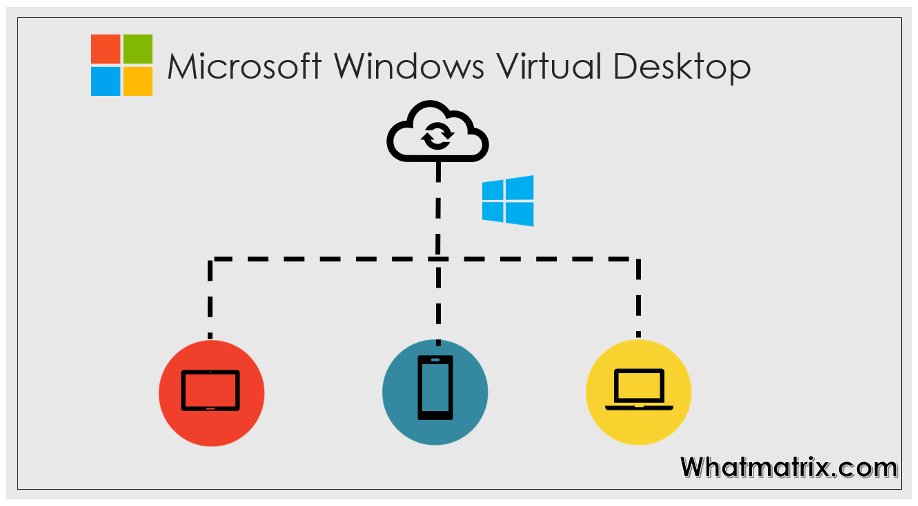
The DaaS Comparison WhatMatrix launched its DaaS (Desktop as a Service) comparison last year initially presenting a comparison of Citrix, VMware, Nutanix and, later that year, added CloudJumper to the mix. The comparison looks at the leading DaaS platforms in the... 
by Community Author | Mar 27, 2020 | Community Updates
Just a quick update. First of all we hope you and your families are OK during this ‘once in a lifetime’ event. We completely understand that priorities have shifted. We only want to assure you that we will remain “open for business” as long a... 
by Community Author | Feb 5, 2020 | CMPs
Landscape Report (Cloud Management Platforms) – what’s needed? This page is intended for vendors who received “notification of inclusion” for a WhatMatrix Landscape Analysis Report. Please see below for instructions on what’s needed and... 
by Dorian Martin | Jan 30, 2020 | Data, Developers
Businesses of all sizes are trying to adapt to the permanently changing technological landscape. One of the recent trends that companies will have to embrace is visual search, which is projected to change the way people look for things on the internet. While tech... 
by Martijn Moret | Dec 17, 2019 | Backup
Meet the vendor: Commvault Our community is glad to announce that Commvault has been successfully evaluated under the WhatMatrix Data Protection criteria. “Complete Backup and Recovery” is now available for (free) comparison and enquiries among other...